Firewall & SSL Solutions
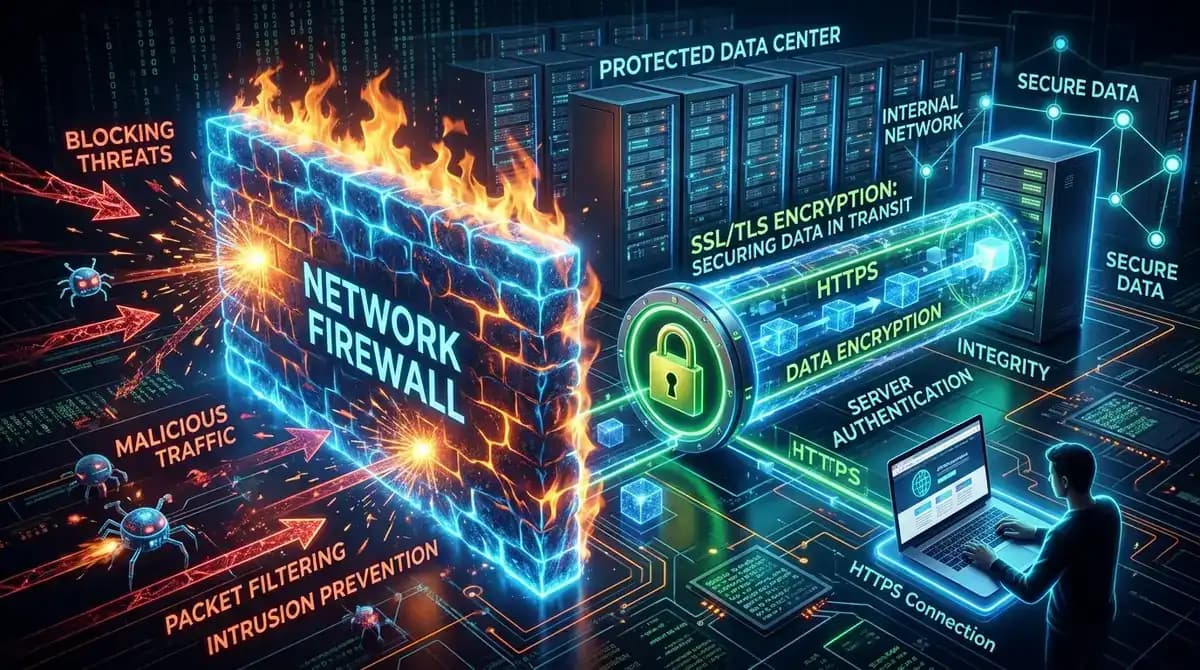
We provide encrypted connections and an impenetrable defense against unauthorized access. We ensure your site operates safely, stably, and with maximum resilience against cyber threats.
Comprehensive Security for Total Peace of Mind
Your website is exposed to constant risks of breaches, data eavesdropping, and malicious traffic. We don't just install certificates - we configure enterprise-grade Firewall systems and TLS/SSL protocols, creating a robust environment that shields your business 24/7.
Full Protection in 8 Strategic Steps
Firewall Deployment
We implement next-generation Web Application Firewalls (WAF) that block malicious traffic at the perimeter. The system monitors for real-time anomalies and automatically thwarts SQL injections and unauthorized intrusion attempts.
Security Rule Configuration
We perform granular request filtering at the server level. We set up IP restrictions, aggressive spam bot protection, and define custom security policies tailored to the specific operational needs of your business.
SSL Certificate Deployment
We ensure a trusted encrypted connection by installing the ideal certificate for your scale (DV, OV, or EV). This guarantees the "padlock" icon in browsers and a secure data exchange between your site and your customers.
HTTPS Migration
The transition to a secure environment must be seamless. We configure precise 301 redirects, fix "mixed content" errors, and ensure that search engines index only the secure version of your site to protect your SEO rankings.
Encryption & HSTS Hardening
We activate HSTS (HTTP Strict Transport Security) protocols - an advanced layer of defense that prevents downgrade attacks and cookie hijacking by enforcing mandatory HTTPS connections.
Malicious Traffic Mitigation
We automatically identify and restrict suspicious requests, botnets, and vulnerability scanners. Our system neutralizes brute-force login attempts at the edge, before they can even impact your server's performance.
Active Security Monitoring
We don't just 'set and forget.' We analyze access logs and monitor for breaches in real-time. Our proactive system triggers immediate alerts and responses upon detecting risks or unusual traffic patterns.
Maintenance & Continuous Updates
Cyber threats evolve daily. We perform regular firewall audits and update security rules to ensure your defensive posture remains resilient against the latest attack vectors.
4 Steps to Total Protection
Analysis
We begin with a comprehensive audit of your current configuration and server environment. We perform deep vulnerability scans to identify critical areas requiring immediate reinforcement. Before we act, we must map every entry point of your 'digital fortress'.
Deployment
We deploy the specialized Firewall layer and the required SSL certificate, perfectly aligned with your hosting and platform. We guarantee zero downtime - your business operations will remain fully functional throughout the entire process.
Optimization & Testing
We fine-tune security rules, migrate all traffic to HTTPS via precise 301 redirects, and rigorously test all contact forms. A full compatibility check is performed to eliminate any 'mixed content' errors and ensure a flawless user experience.
Active Monitoring
Security is a journey, not a destination. Post-deployment, we maintain an active watch. By analyzing attack logs and identifying emerging threats, we provide immediate responses to any suspicious activity or attempted breaches.
Firewall & SSL Protection FAQ
Ready for a more secure website?
Don’t wait for the first breach
Let’s deploy professional protection that encrypts data and guarantees peace of mind for both you and your customers.
